Economics
I don't know about you, but I'm lazy. I always seek a shortcut.
And if there's a shortcut, I won't follow the generic way.
I don't know about you, but I'm lazy. I always seek a shortcut.
And if there's a shortcut, I won't follow the generic way.
Some time ago, I've talked about Tabasco replacements. Several iterations later, I've now arrived at sauces which are are typically placed in the category Inhuman.
On the left, you see three sauces reaching level 10 without extracts. Angry Cock and El Chupacabra are produced by CaJohns in Ohio, while the Jolokia Sauce in the middle is made in Bad Dürkheim by Chili Food. They're all absolutely great, with the latter being particularly fresh and fruity.
On the right, you got two sauces using extract to reach level 10+ (exceeding 250000 Scovilles). Z by CaJohns is a lot like Vicious Viper, but hotter. 😉 Schwarze Witwe is fabricated again by Chili Food and probably the most potent sauce I've ever tried.
The NSA affair continues to make the headlines even three month after the initial report of the report of Glenn Greenwald in the Guardian. Slowly, very slowly, the message of these headlines begins to creep into the consciousness of normal people.
With the result that I'm being asked by an increasing number of people for advice. They always want to know what I'd “recommend”. Recommend with respect to what? As it turns out, most people want to be safe from the spying eyes of the services without changing any of their habits (like skyping and online banking with their trusted Windows XP). They have the most amusing ideas how to accomplish that.
One guy believed he would be safe if he would use his Windows as virtual machine. I tried to discuss this approach, but he insisted, and I thus simply informed him that it is indeed possible to convert a physical Windows installation to a virtual machine. I also told him, as requested, that both VMPlayer and VirtualBox provide convenient point-and-click interfaces with which he can manage his virtual machines. In the course of one afternoon, he converted his existing installation of Windows 7, formatted the disk, installed four different Linux distributions in a row, got VirtualBox running on the fourth, was ignorant about the guest add-ons and was thus shocked to see his Windows running at 1024x768, formatted the hard disk once more and installed Windows again. D'oh! 😄
Others keep asking me about Truecrypt. It's true, everybody seems to recommend Truecrypt right now, even Fefe. I've never used Truecrypt, and I never will. First of all, Truecrypt is not available in the repositories of any of the distributions I'm using (Archlinux, Fedora, OpenSUSE, Debian) since it is not free. Second, the authors of Truecrypt are unknown. I don't see any reason why I should prefer Truecrypt over the better alternatives existing for Linux.
Oh well, there's the culprit. If you want disk encryption for Windows, and are looking for alternatives for BitLocker, Truecrypt appears to be truly attractive.
But seriously: how can anybody aware of the facts still consider using Windows, except as a game starter?
In July, the Guardian has reported that "Microsoft has collaborated closely with US intelligence services to allow users' communications to be intercepted, including helping the National Security Agency to circumvent the company's own encryption [...]." End of July, Heise reported that Microsoft can install root certificates without user intervention by a mechanism called "Automatic Root Certificates Update". In August, the Zeit reported about "Trusted Computing" and the fact that from 2015, a computer with Windows 8 is principally controlled by Microsoft (also read the first paragraph in italics). And in September, Bruce Schneier argues that one should doubt the integrity of commercial, closed-source software in general, and proprietary encryption programs in particular (right, it's a Captain Obvious article).
And at the end of Schneier's article, he says: "And I'm still primarily on Windows, unfortunately." So one can't blame the people, I guess.
Then there are those coming to me since they want to convert to Linux. There's one guy who's using Windows XP, and he asked me if there's a free clone. I could have told him about ReactOS, but I just shook my head. He then asked if there's at least “a Linux without command line”. Literally!
Others just ask me what I'm using. When I tell them that I'm using several different distributions, they are confused. “Why? And which one can you recommend?”
I principally try not to recommend anything. Not because I'm an obnoxious arrogant prick, but because I've learned that my likes and dislikes are incompatible with those of most other people. To be fair, I advice them against Ubuntu, but they install it anyway. Most of them try a few weeks and are then back to Windows, with the sole exception of this little Chinese guy who misunderstood my advice and now calls me the Abanda master. He also calls my Fedora Abanda, the Debian on the workstation Abanda, the OpenSUSE on the servers Abanda, and is always so happy with his little Abanda (aka Ubuntu) world that I never had the courage to disillusion him.
Of all the people talking to me, I had only once the impression that I'm talking to a person who seriously considers a change. “It's not only this NSA business, but even more the dependent position you are in as a Windows user. You always got to accept what MS throws at you, even if you greatly dislike it.”
I gave that person one simple advice, and I repeat it here: If you seriously consider to switch, disregard your previous computer experience, and learn Linux from the grounds up. Install Crunchbang on a virtual machine and work your way through The Linux command line. It will take lots of time (months), but after that, you'll never need Microsoft or Apple again.
It will be your independence day.
For the overwhelming majority of people, surveillance is nothing to worry about. 'If you have nothing to hide, then you have nothing to fear'.
To quote James Corbett: "We've all heard this argument a million times when talking to people about the latest revelations of government snooping or the latest roll-out of creepy Orwellian technology. The implication is that the only people who complain about having their privacy violated are criminals who deserve to have their privacy violated. It is a simple phrase, learned by rote, that is meant to bring the conversation to a close."
Should we let the conversation close at this point? We should not, but how do we refute this statement of the naives and ignorants? They are entirely insensitive to the perpetual violation of our constitutional rights. They don't care that one of the cornerstones of constitutional democracy, 'innocent until proven guilty', has just been twisted around to 'guilty until proven otherwise'. Neither do they think about the future consequences of this paradigm change.
There are a few arguments focusing on the logical and technical aspects of this whole scenario which I find noteworthy.
I know, all of these points are wasted on those who'd need to consider them. Just wanted to list them for memorial purposes.
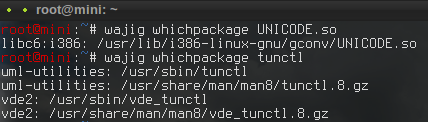
Folding@home or short FAH started in October 2000, and I've joined this concerted effort shortly after. I've contributed to the project ever since, not even stopping once. Despite my humble means, my tenacity resulted in a slow but steady buildup of completed work units. Today, I decided to check my progress and noticed that I've recently entered the top 500 of the FAH community. More precisely, I currently rank 362 of 1700179 with, almost unbelievably, 100 million points:
All these points have been obtained in the honest old-fashioned way: with my CPUs grinding away while the GPUs of other teams danced weightlessly in front of me.
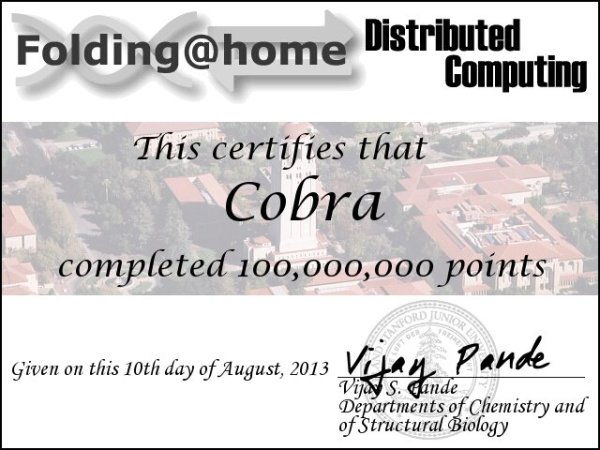
The task: compress data faster than the desktop
The test: compress a 283 MB archive using the fully multithreaded pigz
The result:
0.98 s (4 x Xeon 1240v2 @ 3.4 GHz] 1.42 s (24 x Opteron 8431 @ 2.4 GHz) 1.51 s (24 x Opteron 6176 @ 2.3 GHz)
The conclusion: our next workstation will have Intel CPUs. 😞
If you don't live under a stone, you are sure to have heard about the NSA data affair. All media cover it, and it's on the front page since weeks. You certainly know the term 'whistleblower' by now, and you have an opinion about Edward Snowden, traitor or hero. Perhaps you tend to the latter, and you are now unsure what to do. If so, let me congratulate you. People voting for the former do usually not prove to be particularly pleasant or bright individuals.
I've seen many excellent comments in both newspapers and blogs on the political dimension of this affair, but essentially nothing substantial on the technical aspects. Sure, one can suddenly find all kind of beginner guides to mail encryption, but the views on the effectiveness of this measure vary widely. Self-appointed computer experts, for example, criticize the media for stating that breaking asymmetric encryption takes the NSA "many" years, and boast that it would take them in fact 10290 times the age of the universe for a 2048 bit RSA key.
On the other hand, I've recently overheard the conversation of some young wanna-be scientists, and one of them elaborated on the reasons why encryption is futile. He was quite explicit and stated that the NSA can break any encryption in no more than 10 min, and quoted the "Bergofsky principle".
The "Bergofsky principle"? But of course, how could I forget that: "The principle clearly stated that if the computer tried enough keys, it was mathematically guaranteed to find the right one."
Says Dan Brown in Digital Fortress, St. Martins Press, New York 2000. 😄
In reality, there's of course no "Bergofsky principle", but the exact opposite: mathematically guaranteed unbreakable code since 1882. It's not even that difficult to produce code which is at least close to unbreakable. I will devote one of my future entries to this topic. 😉
Right now, however, we are concerned with the more serious question of how secure conventional e-mail encryption (using PGP or S/Mime) actually is.
Well, regarding conventional (as opposed to quantum) computers, that's public knowledge. Breaking RSA keys takes a certain and documented effort which can even be predicted (asymptotically). RSA-576, for example, was broken in in 2002 after two years of number crunching on the cluster Parnass2 which was listed in the TOP500 in 1999. To break RSA-768 in 2009 required 267 instructions which would have taken Parnass2 more than a hundred years, but took once again about two years of computational effort on a more advanced and larger cluster.
Let me put that into perspective. Parnass2 had a peak performance of 30 GFLOPS (about one third of my current desktop, counting only the processor). The Earth simulator, number one of the TOP 500 in 2002, had 30 TFLOPS, and Tianhe-2, the current number one, 30 PFLOPS. In other words, Tianhe-2 is about one million times faster than Parnass 2. Assuming that the NSA supercomputer under construction is able to deliver a 100 PFLOPS for RSA decryption, we can easily determine the time it would take to break a single RSA key of a given size:
**bits time** 576 3 s 768 30 min 1024 20 days 2048 65 million years 4096 4 billion times the age of the universe
Looks like we are safe from 2048 bits on. But if supercomputers progress like they have in the past, it will take only 65 years to break a 2048 bit key in 2028, and that's cutting it close. And what about quantum computers? D-Wave just sold a number of 512 qubit systems, with Google and NASA being on their list of customers. They announced to have a 2048 qubit version soon. If the D-Wave 2 is a true quantum computer capable of executing Shor's algorithm, messages encrypted with 2048 bit keys are virtual clear text.
Perhaps that's not very likely. But it won't hurt to think about alternative asymmetric encryption algorithms not based on integer factorization or discrete logarithms.
I've been a a hard-core upgrade addict years ago, and that didn't change in the time since then. On the contrary, I've become allergic to outdated software, and I chose the distributions I'm using with particular attention to their closeness to the bleeding edge. I thus run Arch Linux on my desktop, Fedora on my office computer, and OpenSuse on my notebook.
OpenSuse? Bleeding edge?
Well, see for yourself:
With the tumbleweed repository, OpenSuse turns into a really very much up-to-date rolling-release distribution. Definitely worth a try.
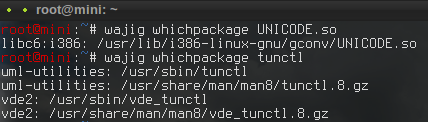
In addition to snapshots of the filesystem, I like to keep a copy of the packages I installed. Fortunately, the package managers of Debian and Archlinux do that by default. After some time, however, this cache occupies a lot of hard disk space. I've thus moved the cache to an external drive for my Mini, but I also don't want to waste precious SSD space on my Desktop just for static packages kept for being on the safe side. How to do that on Arch?
Very simple:
Add
CacheDir = /your/favorite/path
to the [options] section of your /etc/pacman.conf.
If a package misbehaves, you can then easily downgrade by issuing a 'pacman -U '. Up to now, I've needed that only once, but I was happy to have this simple solution at hand.
A recent update of Archlinux moved all binaries to /usr/bin. The update was smooth on my main system, but for my 4 years old virtual Arch, a 'pacman -Qqo /bin /sbin /usr/sbin | pacman -Qm -' revealed that grub 0.97 required a fix.
I could have installed grub-legacy from the AUR, but that idea struck me as a rather backwardish one. Since I learned to really like syslinux from my main system, I installed this modern bootloader instead. Upon a reboot I was greeted with "no operating system found". Hm.
I soon learned that the problem originated from the fact that my /boot partition starts with sector 1. Well, just like fdisk partitioned a few years ago. Now, I could have converted the partition to GPT, but I didn't like that idea too much either. Instead, I tried grub2, only to get rebuffed once more: "no post-MBR gap; embedding won't be possible". Aarghhh!
Finally, it was the Gentoo Wiki which told me what to do: "If you really want blocklists, use --force." A 'grub-install /dev/sda --force' later, my virtual Arch is up-to-date and thus again as new and shiny as in the beginning.